Regedit Commander
A native Win32 registry editor for power-user workflows that exceed the scope of the stock Windows regedit.
Download Latest Release
Platform: Windows x64
Build type: Native C/C++, WinAPI
Status: Pre-release — actively developed, shared for testing
Note: Source code is not published yet. Core features are stable; active work continues on the live monitor engine, and protected-hive diagnostics.
Overview
Building advanced Windows system tooling is mostly an engineering discipline problem, not a UI problem. Regedit Commander focuses on practical workflows: faster navigation, safer bulk edits, dual-pane comparison, and deeper access to protected registry areas — without visual gimmicks.
Features
1. Dual-Pane, Keyboard-First Architecture
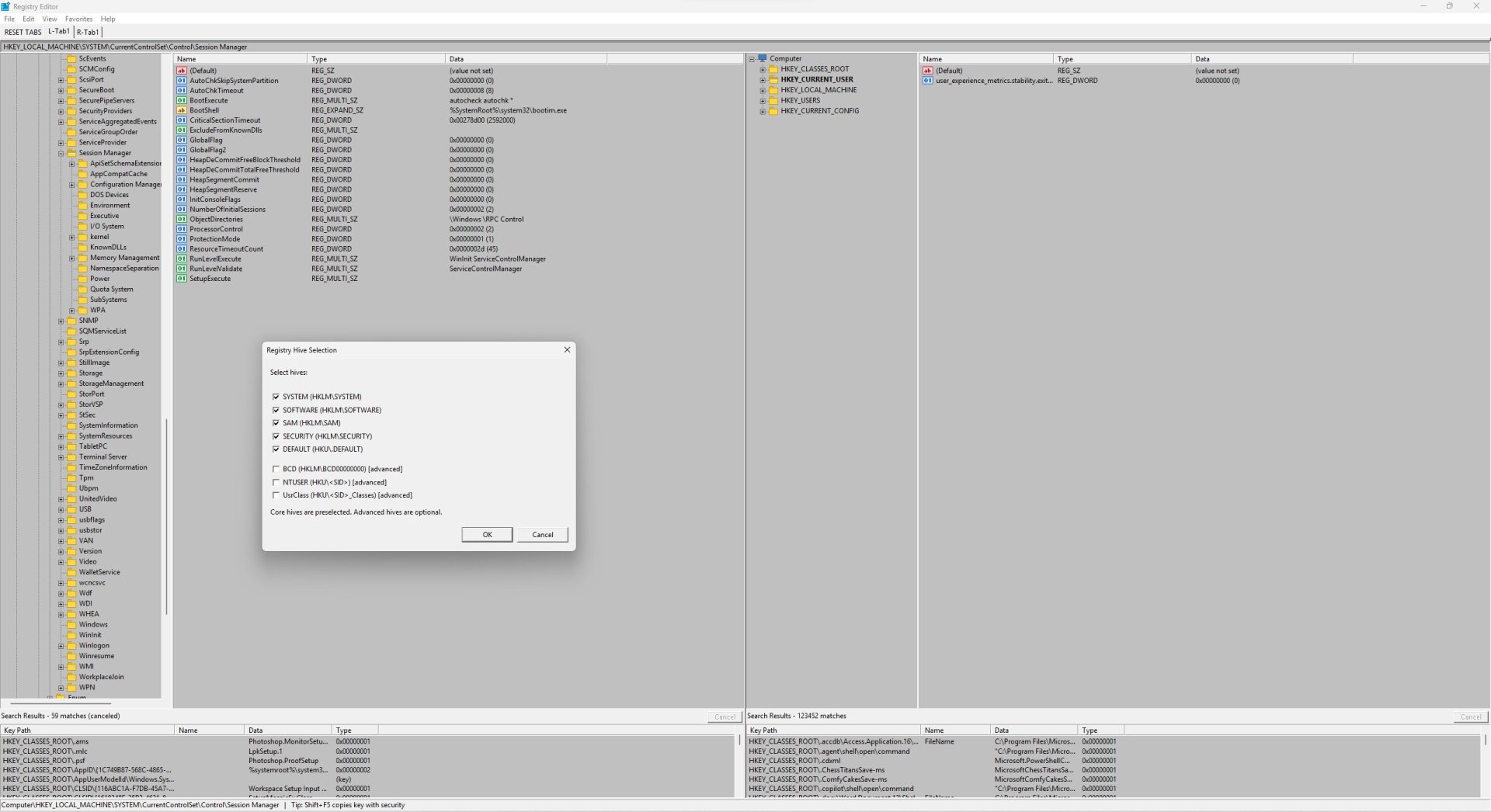
The editor opens in a single-pane mode by default. Press F10 to toggle the dual-pane layout, which gives you independent left and right panels, each with its own key tree, value list, and search results pane at the bottom.
Navigation within a panel uses Ctrl+Tab and Ctrl+Shift+Tab to move focus between the tree view and the value list. Switching between the left and right panels uses Tab. The focus routing is aware of whether the results pane is visible, so keyboard navigation always lands somewhere predictable.
Each panel supports multiple tabs (Ctrl+T to open, Ctrl+W to close). Tab state, including the active key path for each tab, is persisted between sessions. If the tab layout gets cluttered, there is a reset option to return to the default single-tab view per side. Tabs can also be closed via right-click context menu on the tab header.
Cross-panel operations:
| Key | Action |
|---|---|
F10 |
Toggle dual-pane layout on/off |
Tab |
Switch active panel (left / right) |
Ctrl+Tab |
Switch Tree / Value List within active panel |
Ctrl+Shift+Tab |
Switch Tree / Value List (reverse direction) |
F5 |
Copy selected key or value to the other panel |
Shift+F5 |
Copy with full security descriptor (ACL, owner, SACL) |
F6 |
Move selected key or value to the other panel |
Ctrl+T |
New tab in active panel |
Ctrl+W |
Close active tab |
2. TrustedInstaller-Aware Access Model
Standard regedit running as Administrator cannot fully access certain protected branches: SAM, SECURITY, BCD, and other SYSTEM-owned keys. Regedit Commander implements a TrustedInstaller token acquisition path that opens the TrustedInstaller service process, duplicates its impersonation token, and applies it to the thread context before performing protected operations.
This path is used specifically for backup, restore, and export operations on protected hives. The privilege flow is not applied globally — it is scoped to operations that require it, and the original token context is restored afterwards. The implementation lives in TrustedInstallerToken.cpp and requires the process to be running with Administrator privileges as a prerequisite.
This means you can navigate, read, and back up keys like HKLM\SAM, HKLM\SECURITY, and BCD00000000 (mapped as BCD) without needing to manually hack token permissions or use external tools.
3. Hive-Level Backup and Restore Engine
This is not .reg file export/import. The backup engine uses the native RegSaveKey / RegLoadKey / RegReplaceKey API path, which operates on raw hive files — the same format Windows uses internally.
Backup workflow:
Select the hive set you want to back up (SYSTEM, SOFTWARE, SAM, SECURITY, NTUSER.DAT, BCD, etc.) and choose a base output folder. The engine automatically creates a timestamped subfolder named Registry_Backup_YYYYMMDD_HHMMSS inside that folder. Each selected hive is saved as a binary hive file in that folder. The backup uses SeBackupPrivilege and TrustedInstaller context where required.
Restore workflow:
Select a previously created backup folder and choose which hives to restore from it. The restore uses RegReplaceKey with a .TMP + .BAK staging strategy: the replacement is scheduled at the kernel level and takes effect after a reboot. The old hive is retained as .BAK until the new one is confirmed. After successful scheduling, the tool optionally prompts for an immediate reboot.
Restore folder history is saved in the application settings, so frequently used backup locations appear in a dropdown for quick reselection.
| Key / Menu | Action |
|---|---|
| Menu: Backup | Select hives and destination folder, run backup |
| Menu: Restore | Select backup folder and hive set, schedule restore |
4. Search, Find All, and Replace
Find / Find Next (Ctrl+F / F3) — standard incremental search with match-case and whole-string options.
Find All (Ctrl+Shift+F) — runs a background search across the entire selected subtree. Results appear in the dedicated Search Results pane at the bottom of the active panel. In dual-pane mode, each panel has its own results pane. The search is non-blocking: the UI remains responsive while results stream in, and there is a cancel path to stop an in-progress search. Results can be exported as TSV, CSV, UTF-8, or UTF-16 paths.
Replace (Ctrl+H) — the replace dialog supports:
- Targeting value names, value data, or both
- Single replace and replace-all
- Preview before commit — you see what will change before anything is written
- Match-case and whole-string match options
- Regex mode using ECMAScript-style semantics (the same engine used by
std::regexwithECMAScriptflag)
Regex replace works on both value names and value data. The preview step is mandatory for replace-all; there is no way to commit a bulk replace without reviewing the diff first.
| Key | Action |
|---|---|
Ctrl+F |
Find |
Ctrl+Shift+F |
Find All (background, results pane) |
F3 |
Find Next |
Ctrl+H |
Replace (with preview) |
5. Diff and Live Monitor
Compare Keys — with dual-pane open, navigate to a key in the left panel and a different key in the right panel, then invoke the compare command. The value list uses custom-draw rendering to highlight differences:
- Values present only in the left key are marked as left-only
- Values present only in the right key are marked as right-only
- Values present in both but with different data or type are marked as changed
The diff table is built by enumerating both key handles, sorting by name, and performing a merge-compare pass. Type mismatches are treated as changes regardless of data content.
Live Monitor (Ctrl+M) — opens a separate monitor window for the currently selected key. The monitor thread uses RegNotifyChangeKeyValue with a stop event to detect changes, then takes a snapshot of the key's values and subkeys and compares it against the previous snapshot using a FNV-1a hash per value's data buffer. Changes are logged to a text output in the monitor window with timestamps. The log is trimmed automatically when it exceeds 200,000 characters to prevent unbounded memory growth. The monitor window can run in coarse mode (batching rapid notifications) or precise mode.
| Key | Action |
|---|---|
Ctrl+M |
Open Live Monitor for selected key |
6. Undo/Redo and Binary Editing
Undo/Redo — destructive operations (create, delete, rename, edit value) are recorded in an undo history. Ctrl+Z / Ctrl+Y step through the history. For subtree-level operations, value snapshots are stored in memory before the operation, allowing full rollback. An undo history dialog is available for viewing and selective rollback.
Binary / Hex editor — double-clicking a REG_BINARY value opens a built-in hex editor dialog modeled after HxD-style interaction: byte-level cursor navigation, offset display, ASCII pane, and direct editing. For non-destructive inspection of any value's raw bytes, a separate Display Binary Data path is available from the context menu — this opens a read-only hex view without entering edit mode.
| Key | Action |
|---|---|
Ctrl+Z |
Undo |
Ctrl+Y |
Redo |
7. Other Operations
| Key | Action |
|---|---|
F7 |
Create new key |
F2 |
Rename key or value |
Delete |
Delete selected key or value |
Ctrl+R |
Refresh current view |
Ctrl+C |
Copy key name / value data to clipboard |
Additional operations available via context menu: copy full key path, open permissions dialog (ACL editor), connect to remote registry, export subtree.
Keyboard Reference
| Key | Action |
|---|---|
F10 |
Toggle dual-pane layout |
Tab |
Switch active panel |
Ctrl+Tab |
Switch Tree / Value List |
Ctrl+Shift+Tab |
Switch Tree / Value List (reverse) |
F5 |
Copy to other panel |
Shift+F5 |
Copy with security descriptor |
F6 |
Move to other panel |
F7 |
New key |
F2 |
Rename |
Delete |
Delete |
Ctrl+F |
Find |
Ctrl+Shift+F |
Find All |
F3 |
Find Next |
Ctrl+H |
Replace (with preview) |
Ctrl+T |
New tab |
Ctrl+W |
Close tab |
Ctrl+M |
Live Monitor |
Ctrl+R |
Refresh |
Ctrl+Z |
Undo |
Ctrl+Y |
Redo |
Requirements
- Windows 10 or Windows 11 (x64)
- Administrator privileges required for protected-hive operations
- No external dependencies — single executable
Important Notes
- Backup, restore, and TrustedInstaller operations are powerful. Test on a VM before using on a production system.
- The restore mechanism schedules hive replacement via
RegReplaceKey; changes take effect after reboot. - Behavior may differ across Windows builds. Bug reports with Windows version and exact reproduction steps are very welcome.
- The BCD hive is mapped as
BCD(restored fromBCD00000000).
License
This software is provided for personal and home use only.
- You may use this software on your own personal computers for non-commercial purposes.
- You may not redistribute, sublicense, sell, or incorporate this software into any commercial product or service.
- You may not reverse engineer or modify the software.
- Source code is not provided and remains proprietary.
Copyright (C) 2026 Marek Wesolowski (wesmar). All rights reserved.
Feedback
This is a pre-release build. If something breaks — especially around restore scheduling, TrustedInstaller token handling, or monitor behavior on specific Windows builds — please open an issue with your Windows version, build number, and steps to reproduce.